
Secure Your Digital Future with Intelligent Defense
Advanced threat detection meets user-friendly simplicity. We provide the tools you need to safeguard your privacy and data against evolving cyber risks in a connected world.
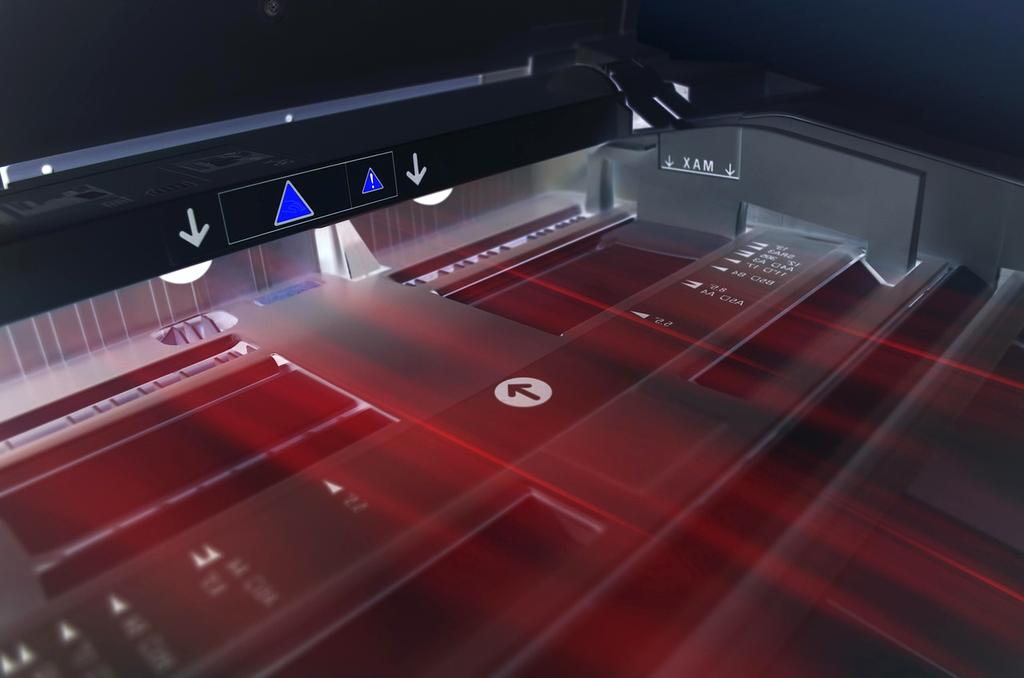
AI-Driven Defense Matrix
Our autonomous neural networks predict and neutralize threats before they materialize, ensuring zero-trust integrity across all endpoints.
Predictive Behavior Analysis
Real-time anomaly detection using heuristic algorithms that learn your unique digital footprint to flag irregularities instantly.
Neural Interception
Deep learning protocols that intercept malicious payloads at the packet level, rendering them inert before execution.
Post-Quantum Cryptography
Future-proof encryption standards designed to withstand computational power from next-generation quantum processors.
Live Threat Landscape
Monitoring global vectors 24/7.

Immutable Digital Identity Verification
Replace vulnerable passwords with living cryptographic keys. Our decentralized identity framework uses biological and behavioral markers to create a security perimeter that cannot be phished, shared, or stolen.
Liveness Detection
Active sensing algorithms distinguish biological tissue from synthetic replicas, preventing spoofing attempts with 99.99% accuracy.
- Pupil Dilation Tracking
- Skin Texture Analysis
- Micro-Expression Mapping

Sovereign Data Control
Your identity credentials are stored locally on your device, not on a central server. Verification happens via zero-knowledge proofs.
Alex Cipher
ID: 8X-992-Alpha
Initiate Secure Handshake
Establish a direct encrypted line with our defense architects. Your transmission is protected by 256-bit AES protocols.